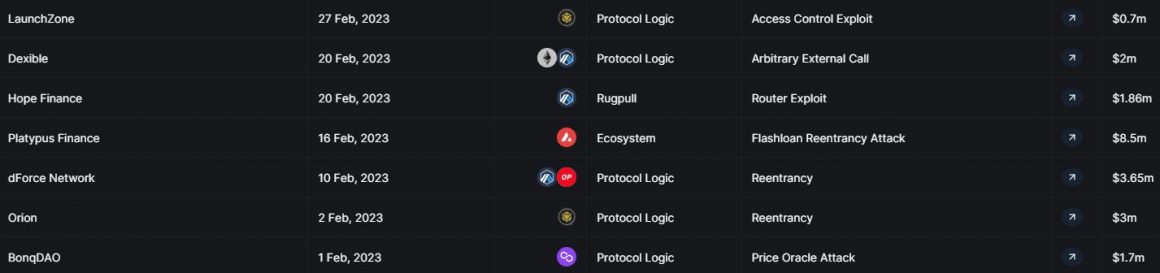
DeFi platforms lost over $21 million to hackers throughout February, according to data released by DeFi project aggregator DefiLlama.
Reentrancy, price oracle attacks and exploits across seven protocols caused decentralized finance (DeFi) space to bleed at least $21 million in crypto in February.
According to DeFi-centric data analytics platform DefiLlama, one of the largest in the month was the flash loan reentrancy attack on Platypus Finance, which led to $8.5 million of funds lost.
DefiLlama highlighted six other noteworthy hacks in the month, the first being the price oracle attack on BonqDAO on Feb 1.
BonqDAO: $1.7 million
BonqDAO revealed to its followers in a Feb. 1 post that its Bonq protocol was exposed to an oracle attack that allowed the exploiter to manipulate the price of the AllianceBlock (ALBT) token.
The exploiter increased the ALBT price and minted large amounts of BEUR. The BEUR was then swapped for other tokens on Uniswap. Then, the price was decreased to almost zero, which triggered the liquidation of ALBT troves.
Blockchain security firm PeckShield estimated the losses to be around $120 million, however, it was later revealed hackers reportedly only cashed out around $1 million due to a lack of liquidity on BonqDAO.
Orion Protocol: $3 million
Just a day later, decentralized exchange Orion Protocol suffered a loss of roughly $3 million on Feb. 2 through a reentrancy attack, where attackers used a malicious smart contract to drain funds from a target with repeated withdrawal orders.
Instead of relying on low-impact bounty programs, our own funds were used in our smart contracts as a way to attract Web3's most sophisticated hackers. Of course, we always hoped that a vulnerability would not be found.
— Alexey Koloskov (@alexeykoloskov) February 2, 2023
Orion Protocol CEO Alexey Koloskov confirmed the attack at the time, assuring everyone, “All users’ funds are safe and secure.”
“We have reasons to believe that the issue was not a result of any shortcomings in our core protocol code, but rather might have been caused by a vulnerability in mixing third-party libraries in one of the smart contracts used by our experimental and private brokers,” he said.
dForce Network: $3.65 million
DeFi protocol dForce network was another February victim of a reentrancy attack resulting in losses of around $3.65 million.
In a Feb. 10 post, dForce confirmed the exploit; however in a twist, all funds were returned when the hacker came forward as a whitehat hacker.
2/5 Shortly after the incident, we entered into conversations with the exploiter, who came forward as a whitehat. We have agreed to offer a bounty and will drop all on-going investigation and law enforcement actions.
— dForce (@dForcenet) February 13, 2023
“On Feb. 13, 2023, the exploited funds were fully returned to our multi-sig on both Arbitrum and Optimism, a perfect ending for all,” dForce said.
Platypus Finance: $9.1 million
On Feb. 16, DeFi protocol Platypus Finance suffered a flash loan attack resulting in $8.5 million being drained from the protocol.
A post-mortem report from Platypus auditor Omniscia noted that the attack was possible because of code in the wrong order.
On Feb. 23, the team announced that they are seeking to return around 78% of the main pool funds by reminting frozen stablecoins.
https://twitter.com/Platypusdefi/status/1631573948147306497?ref_src=twsrc%5Etfw%7Ctwcamp%5Etweetembed%7Ctwterm%5E1631573948147306497%7Ctwgr%5E36056006f63d066e22dd2fe5293d4b0fd4b33fe0%7Ctwcon%5Es1_&ref_url=https%3A%2F%2Fcointelegraph.com%2Fnews%2F7-defi-protocol-hacks-in-feb-sees-21-million-in-funds-pilfered-defillama
The team also confirmed second and third incidents, which led to another $667,000 exploited, bringing total losses of around $9.1 million.
French police arrested two suspects related to the hack and seized around $222,000 worth of crypto assets on Feb. 25.
Hope Finance: $1.86 million
A few days later, users of arbitrum-based algorithmic stablecoin project, Hope Finance, fell prey to a smart contract exploit on Feb. 20, which saw roughly $2 million stolen from users.
#CommunityAlert 🚨@hope_fin have announced the community has been scammed for ~$2m making this the largest #exitscam on Arbitrum in 2023.
$1.86m was transferred to @TornadoCash.
Hope_fin have posted steps for user's to withdraw their staked LPhttps://t.co/hJbFXiKujt
— CertiK Alert (@CertiKAlert) February 21, 2023
Web3 security firm CertiK flagged the incident on Feb. 21, following an announcement from the Hope Finance Twitter account notifying users of the scam.
A member of the CertiK team told Cointelegraph at the time that the scammer had changed the details of the smart contract, which led to funds being drained from Hope Finance genesis protocol:
“It appears that the scammer changed the TradingHelper contract which meant that when 0x4481 calls OpenTrade on the GenesisRewardPool the funds are transferred to the scammer.”
Dexible: $2 million
Multichain exchange aggregator Dexible was hit by an exploit that targeted the app’s selfSwap function, with $2 million worth of cryptocurrency was lost as a result of the Feb. 17 attack.
According to a Feb. 18 post from the exchange, “a hacker exploited a vulnerability in our newest smart contract. This allowed the hacker to steal funds from any wallet that had an unspent spend approval on the contract.”
Dear Dexible community, we regret to inform you that in the early hours of February 17th, a hacker exploited a vulnerability in our newest smart contract. This allowed the hacker to steal funds from any wallet that had an unspent spend approval on the contract.
1/5
— Dexible (@DexibleApp) February 17, 2023
After investigating, the Dexible team found that an attacker had used the app’s selfSwap function to move over $2 million worth of crypto from users that had previously authorized the app to move their tokens.
After receiving the tokens into their own smart contract, the attacker withdrew the coins through Tornado Cash into unknown BNB wallets.
LaunchZone: $700,000
BNB Chain-based decentralized finance (DeFi) protocol LaunchZone had $700,000 worth of funds drained on Feb. 27.
According to blockchain security firm Immunefi, an attacker leveraged an unverified contract to drain the funds.
“An approval had been made to the unverified contract 473 days ago by the LaunchZone deployer,” Immunefi said.
The February figures are a stark increase from January, according to DefiLlama figures.
The tracker lists only $740,000 in hacks to DeFi platforms in the month across two protocols — Midas Capital and ROE Finance.
In its 2023 Crypto Crime Report, blockchain data firm Chainalysis revealed that hackers stole $3.1 billion from DeFi protocols in 2022l, accounting for more than 82% of the total amount stolen in the year.



